Confuse the different types of proxy servers? For all the technical and computer enthusiasts out there, the term “proxy” is nothing new. Yet for those of you who are not very well acquainted with this, do read on and get ready to be mesmerized by what a wonderful facet of technology it is.
Table of Contents
What is a proxy?
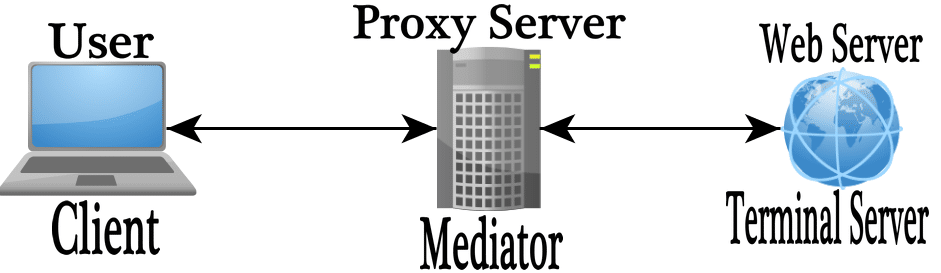
In order to better understand what a proxy is, you have to be well versed with the term “intermediate”. Simply put, an intermediate is a bridge that connects two routes or paths in a cycle or process. An intermediate, in addition to bridging the gap between two systems, can also serve a vast array of functions that are central to the process that the two systems are involved in.
Now let’s connect the two dots. A proxy is fundamentally an intermediate that allows you to access information over the internet. A proxy is a really handy companion when it comes to this task because whenever you search something over the internet, you are essentially requesting to see some specific piece of information. The proxy server processes this request and uses it to give you the results that you were seeking.
But this is a very one-dimensional idea of what a proxy is. Read on further in order to get a better-rounded image of this term.
How Proxy Server Works?
Now you have already known that A proxy or a proxy server (in a very formal sense) is another computer that acts as an intermediate between the basic computer that you are using and the realm of web browsing.
Let me take “search on Google” for example, What a proxy server does is that when you enter a particular search term on Google, that search term is processed as a request for information, This request is then passed to the proxy server which in turn passes it on to the entire internet network. When this happens, the search terms that you entered are used to retrieve information.
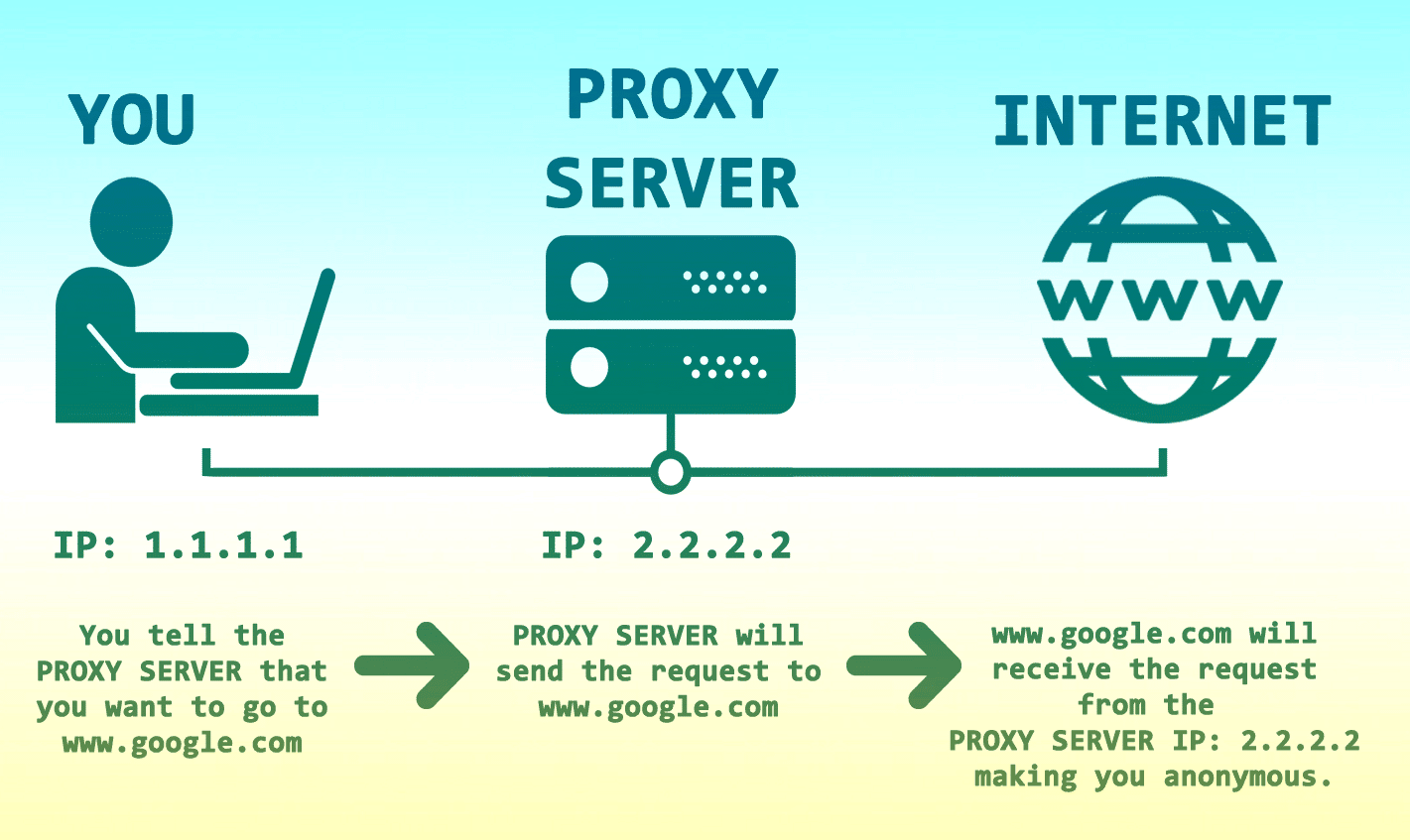
This information is then returned to the proxy server which then passes it back to your basic computer. As long as this process sounds, it is quite similar to how our body reacts to a painful stimulus in terms of speed, meaning that it is a really rapid process.
But a proxy is not just an intermediate. It is a device for sustaining anonymity. A proxy server, upon processing the request, filters out the valuable data (such as your IP address) which prevents people from looking you up based on your search results. Most proxies are configured to act in such away. This is what makes it different from a standard, direct connection between your basic computer and the web browsing network.
Invention of Proxy
Proxies were initially invented for the purpose of giving structure to distributed systems, but they have come pretty far from that function and have developed into full-fledged technical intermediates that have greatly simplified the complex task of researching and information gathering over the internet. These proxy servers are the reason as to why people today are so easily able to look up information for their projects and assignments with the simple push of a few keys.
When discussing proxies, it’s vital to understand “Forward Proxies” & “Reverse Proxies”. To understand Forward & Reverse proxy, it’s important to understand the term Proxy in simple terms, before going into a much more detailed definition. Using a proxy is simply equivalent to someone doing something on your behalf. Basically, a server acting on the behalf of another computer to perform the tasks you wish to do with the objective to mask the identity of the actual user/visitor. In layman terms, The difference between the two is that the objects of the proxy are different:
The object of the forwarding proxy is the Client, and the object of the reverse proxy server is the server.
Forward Proxy Server
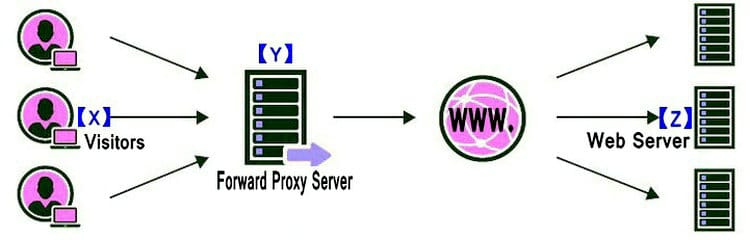
The Y – “administrator of proxy server” can use Forward Proxy to,
- Block the users from visiting specific sites e.g: social networks, explicit sites etc.
- Monitor the activity of the users. E.g: monitor what your employees are doing.
When discussing web proxies, we usually are referring to forward proxies. Its work is to retrieve data from another web site on the behalf of the original user. In simple terms, let me explain it this way. Suppose there are 3 devices connected to the web.
X = Visitor’s device, Y = Forward proxy server, Z = Web server – The website you want to visit.
Normally, without proxy the connection established would be from X to Z. However, in some cases, it’s better for Y to connect to Z on behalf of X, which is the basic working of a proxy. But you’re probably wondering why “X – Visitor” uses forward proxy? The reasons can be due to the following:
- Unblock websites. Wanting to visit a site that’s blocked or banned by the ISP, government or Internet administrator. E.g: social networks, that mostly are banned in institutes. With a forward proxy, you may be able to connect easily;
- Bypass Restrictive Limits. The administrator of Z (the site to visit) has blocked or banned X. E.g; you just got banned from a forum for spamming, in that case, to overcome the ban – you may want to use a forward proxy.
- Anonymous Browsing to protect your privacy.
So, The X – “Visitors” can use a free or paid Forward Proxy Server for masking their IP address to access Z – “the web server” which you’re want to visit.
Hopefully, that was enough explanation in simple terms, now to elaborate forward proxy.
A forward proxy is the type of proxy that has been configured in such a way that it handles or processes the requests of a single client or a group of different clients under the control of a local administrator and passes on these requests to a group of resources that are beyond the administrator’s control.
To simplify this definition, let’s take the example of a waiter serving the customers of a restaurant. The waiter takes the orders of different customers and passes them onto the chef who prepares the food, hands it back to the waiter who serves it to the customers. In this case, the customers are the clients, the waiter is the administrator and the chef is the resource.
So a forward proxy is essentially the same as a regular proxy, however, sometimes it is named like this for the sake of technical distinction.
Read More, Guide to find Top Forward proxy providers for your online activities.
Reverse Proxy Server
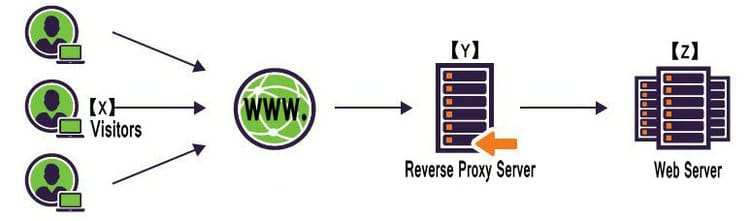
The Z – “administrator of web server” Use Reverse Proxy servers to,
- Cache Content
- Scrub Traffic
- Mask your IP of web Server
- Improve site speed through CDN.
For the sake of explaining reverse proxy in simple terms, let’s take the example of 3 devices connected to the Internet once again, where X = your device, Y = the proxy server, Z = the site you want to visit.
In normal circumstances, the user would connect directly from X to Z. However, in some scenarios, it’s better for admin of Z to block direct access and go through Y first. Just like before, data is being retrieved by Y -> Z on behalf of X.
You’re still probably confused as this may seem the same as a forward proxy, as that’s not true. The user, in this case, connecting to Z does not know he’s accessing Z (the website), because he’s only communicating with Y. Hence the server Z is invisible to the user and the only Y is visible to it externally. We can conclude that a reverse proxy does not need a proxy configuration from the client’s side, as that’s already taken care of.
The client’s believed to be interacting only with Y, however, that’s not true as in reality that Y is forwarding all its communications to Z.
You’re probably wondering why would one want to use a reverse proxy? Here’s as follow:
- Z wants to make sure all the visitors that visit its site are forced to pass through Y first. The biggest example of this is CDN (Content Distribution Network) which is widely spread in the majority of the popular sites to increase speed. What’s happening here is that Z sets up many servers, puts up a reverse proxy so that the user will be sent to the server closest to them when they visit Z (the website.)
- The admin of Z fears that exposing the main server may open it up to intruders to the content hosted.
Types of Proxies
So now that you have a broad idea as to what a proxy server is and There are lots of different type of proxy servers, it’s time for you to look into the various types of proxy servers that exist,
Proxies Classify by Internet Protocols
Not all proxies are the same, they all vary in respect to speed, security & routing protocols. Proxy is further classified into two types, which is HTTP (Hyper Text Transfer Protocol) & SOCKS (Secure Socket) technology.
Though We’ve already discussed the HTTP Proxies and SOCKS Proxies on the previous post, let me show more details about that.
Usually, the difference between proxy servers is applied to protocols & technologies. An HTTP proxy is the most popular, as it’s commonly used around the world by a majority of the users for surfing the net. Free Public proxies, private proxies & few VPN services almost use HTTP proxies. The reason for its popularity is due to the fact that it was built especially for surfing the Internet initially, hence why it’s compatible to work with any browser. After a while, it was upgraded & now is able to works with various other applications thanks to the SOCKS technology.
And one of the most different between the socks proxy and HTTP proxy is, socks proxy can use on lots of different application, HTTP proxy can ONLY be used to handle HTTP request, the socks proxies can be used to FTP, ICQ MSN, Outlook, TheBat, Skype..and so on, And the commonly used ports of the proxy server are,
- Ports of HTTP Proxy: 80/8080
- Ports of SOCKS proxy: 1080
It is a proxy which facilities the practically of any application via a proxy server. During the start, browsers didn’t work with the SOCKS technology hence why they required special applications in order to facilitate the working with proxies. Users tend to use SOCKS proxies due to the reason, SOCKS technology can work on any network protocol and on any port, unlike HTTP proxy which is tied to the HTTP protocol. However, when both HTTP and SOCKS proxies are compared security-wise, SOCKS proxies tend to do much better in security,Okay let me show you the More details,
HTTP Proxy
An HTTP proxy is a proxy server which handles the HTTP(S) requests, For the HTTP proxy only handle the web applications, which named by other as web proxy server. And the HTTP proxy server provides an extra layer of security as the actual web servers cannot be directly reached, only requests on certain IPs and ports are gone through.
A load balancer is a good example of a web proxy. From the above, we can conclude that HTTP(S) proxy acts a middle man between you and the website you’re visiting in simple terms. On the Internet, there are many HTTP(S) proxy servers online.
An HTTP proxy server is a server that is used to process the HTTP requests, which use the format the IP:Port. In these proxies, the request made by the client is passed on in the form of a complete URL. When this URL is passed on, the proxy makes the request more specific in order to retrieve the most relevant search results only. The basic mechanism for maintaining the anonymity of the user is conserved such that not you, but the web proxy server is connecting to the website. This acts as a shield between you and the website you are accessing, thereby preventing anyone from looking up your online activity.
-
How to install squid HTTP proxy on Linux
Usually private proxy service Use Squid to create HTTP proxies on Debian/Ubuntu/Centos.
Now there are lots of guide about “How to set up a private proxy” on Linux,
Here is a guide about “How To Install Squid Proxy on CentOS 6” by the digital ocean, Another guide about “How to Create an HTTP Proxy Using Squid on Ubuntu” by Linode, Also here is a tutorial video,

If you’re good at on coding, which is really not difficult to set up, at generally a IP address cost $0.9 – $3, on the basis of how many IP addresses you want to purchase, if you’re tired on the code or don’t want to take time to do that, you can easily find that proxy service online, which offer different package to use.
Read more, 5 Best Dedicated Proxy Providers
-
How to install HTTP proxy on Windows
And do you want to let you PC(windows) as an IP: Port proxy server, here let me show you how to set up on your windows PC, and Here is video showing what is the web proxy server and step to step,
- How to set up web proxy server Using Internet Information Services (IIS) with application request routing configured (ARR)
The Internet Information Services or IIS feature is an extensive web server that has been created by Microsoft. The purpose of this server is to make the complex task of rerouting URL requests easier for their clients. Setting up this feature, coupled with the use of an efficient proxy server will allow you to make the best possible use of your computer as well as your time.
The process is rather simple, but a bit lengthy, hence do pay close attention to what you are about to read from this point onwards:
Firstly go to the Control Panel of your computer. Click on “Items” and then go to “Programs and Features.” There will be an option available for you to turn on the “Windows Feature”. This is what you must activate. Thereafter a prompt will show up asking you if you wish to enable the Internet Information Services feature or not.
Once you enable this feature, expand the entire window. Then go to “Web Management Tools.” Go to “Common HTTP Features” and choose “HTTP Redirection”. Don’t make any further changes and simply close the window. It will then start installing the files for your IIS feature. This will take a few minutes at most (unless your computer needs improvement). This will now activate your IIS feature and it can act as a web proxy that is now capable of rerouting and better processing your HTTP requests.
However, the process is not done yet. While the IIS feature does give us the ability to reroute the HTTP requests that we make, we need a feature that will allow us to rewrite the URLs such that we can reroute our requests according to our own needs. And the feature that caters to this particular need is the ARR (Application Request Routing) feature. If we go to “Downloads” or if we simply open our “IIS Manager” – we will find that there are no ARR or URL Rewrite features that are needed for changing the URL between our internal and external domains. (Domains refers to the computers that the proxy or feature connects)
In order to install this feature, we will look it up on the Microsoft website. A relevant search will lead us to a page with a download option for this feature. Click on the option and from there a prompt will appear which you can both save and then run on your computer or run directly over the internet. Thereafter, the files for this feature will be installed. One of these is the “Web Platform Installer”. Launch this installer and it will give you the option of installing ARR feature from a list of features. You will find that there are many different variants of this feature present on the list. Each of these variants is meant to cater to the bifurcated configurations of computers that exist.
Don’t panic if you don’t have a good idea regarding your computer’s specifications. Select the ARR 3.0 and the URL Rewrite 2.1 features. These are the most accommodating variants on the list. A dialog box will appear to confirm your selection of the program. Check to see if it displays your selected programs and then confirm it. Thereafter, the files for these features will be installed on your computer on their own. This will take a few minutes at most. Thereafter, if you check the Internet Information Services Manager on your computer, you will see both the URL Rewrite 2.1 and the Application Request Routing (ARR) 3.0 features.
If these features are not present, then you might want to look back at the installation process to see if you missed out on a step.
Socks Proxy
A Socks Proxy or a Socks Server is a general-purpose proxy server. It is capable of routing traffic back and forth between the client and the external server to which the requests are sent by means of a special connection known as a TCP connection. The best part about this type of server is that it is able to cater to any network protocol (not just the HTTP) making it a very versatile and efficient server to be used. However, unlike the Web Proxy server, which makes the URL requests more specific, the Socks Proxy regulates the request as it is without making any changes to it. It is typically used by people to by-pass firewalls in order to access programs on an external resource.
However, in order to activate this feature, the browser that is being used must be configured in such a way that it is “SOCKS enabled.” This will allow the browser you are using, to connect to a Socks Proxy or a Socks Server which grants the browser itself, the ability to transcend firewalls and access programs. Don’t worry, if all this sounds too complex. It is relatively easy to activate and use.
When it comes to deciding between HTTP & SOCKS proxy, users tend to look at the speed factor. This shouldn’t be actually considered a factor as in reality, there’s only a very slight speed difference and speed entirely depends on the company providing these technologies. When it comes to coding, SOCKS technology is much simpler, since they don’t have much code and can transfer & download data slightly faster as compared to HTTP. In the end, it all comes down to personal preferences.
When working with various different applications, it’s important to note which one of these proxies will be able to work. Most applications work with HTTP proxies, however, that’s no reason to rule out SOCKS proxy as it is good to do a bit research as some applications do tend to work with them. Some examples of the applications that work with SOCKS are FTP, ICQ, MSN, Outlook, Skype, etc.
-
How to set up SOCKS5 Proxy Server
The easiest way to create a SOCKS5 Proxy Server is, Find a web hosting or VPS which support the SSH, And via this SSH tunnel set up as secure SOCKS proxy, then you can use your browser to access the server by Putty, Here is the tutorial,
- Set up a SOCKS proxy on a Linux server with SSH
- How to use Putty and SSH tunnel as a secure SOCKS proxy
And There is a video guide to configuring and setting up a Socks5 Proxy using a CentOS 7 on the AWS(Amazon Web Services) platform.

Proxies Classify by IP address
There mainly two types of forward proxies Classify by the type of IP address, the Residential IP Proxy, and Datacenter IP Proxy. When using the proxy server, It’s import to choose either use a Datacenter IP or a Residential IP, which type of IP address you want to use, let me do a concise explanation to you,
Data Center IP Proxy
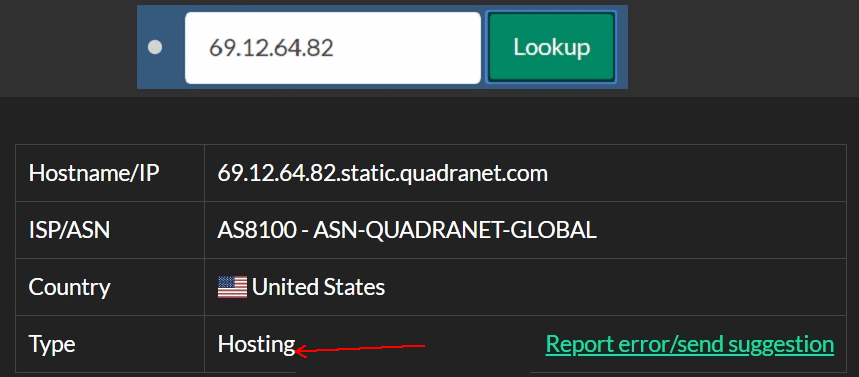
DataCenter proxies provide IP address from company or Corporate of Hosting or other web service, Such as, Amazon Web Services (AWS), Microsoft Azure Cloud, Vultr, DigitalOcean and so on, The Corporate rent lots of IPs and get the most fast and stable Internet connection from Internet Service Provider (ISP) of Data Centers.
With those Hosting or dedicated company, lots of proxy providers or marketers rent the dedicated server and set up the proxy server on a dedicated server, then rent and assign the IPs to each proxy, usually, 1 IP cost $2, and the Data Center IP Proxies are also known as the dedicated proxies,
- Hard to detect the Residential IP Proxy
- No need to care the IP/IP address be banned
- Getaway proxy server Rotate the IPs all the time
- Speed is slower than dedicated proxy
- Hard to continuously use a fixed IP address
- P2P Proxy network is a little danger to use
Residential IP Proxy
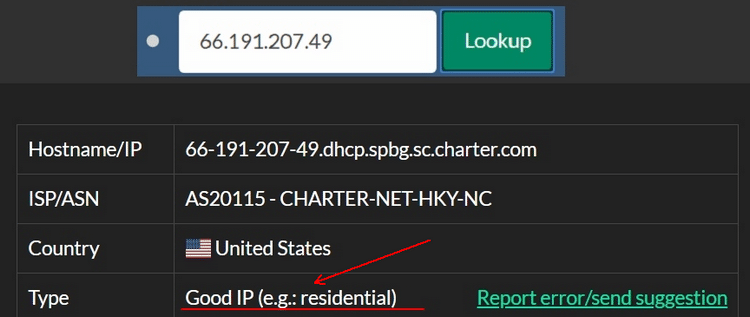
Residential proxies provide IP address from an Internet Service Provider (ISP) that is wired directly into your home or to a cable or DSL. All those who use the internet, be it an individual or a business, requires a residential IP address. When the user makes use of the residential IP proxy, the proxy provider will be lending you its IP address as it connects you to its ISP. Now you borrow the address and location of the ISP provider, while your very own location remains safe,
- Hard to detect the Residential IP Proxy
- No need to care the IP/IP address be banned
- Getaway proxy server Rotate the IPs all the time
- Speed is slower than dedicated proxy
- Hard to continuously use a fixed IP address
- P2P Proxy network is a little danger to use
Data Center IP proxy/dedicated proxy generally offers a fixed IP:Port to use.
Residential IP Proxy generally offers a Getaway proxy server (***.com:Port) to use.
Other Proxies
DNS Proxy
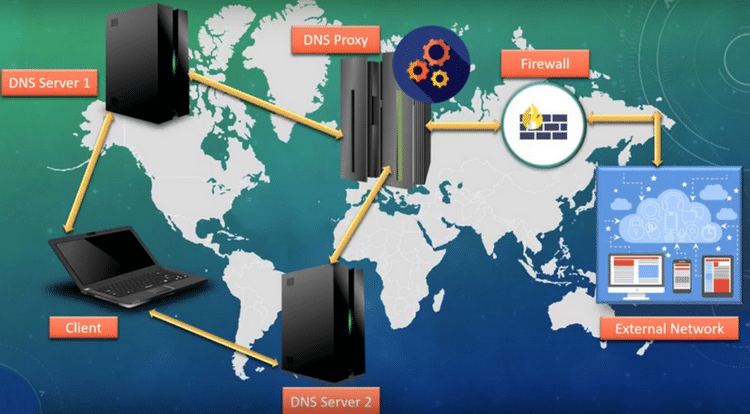
DNS stands for the domain name system, the DNS proxy also knows as the dynamic name system proxy, When As the name suggests, this is a very dynamic proxy and can be used for a wide variety of purposes. It has several features that make it quite a popular name on this list of proxies. The most prominent feature is that of DNS Proxy Cache. Whenever a DNS proxy resolves or passes on a request from the user, it stores the said request in its cache data.
-
The DNS proxy relays DNS requests to the current public network DNS server,then DNS proxy server transfer the replies to the client device.
-
Though the DNS proxy use Cache, The DNS proxy is tracking the public DNS requests to monitor the configiration if previous resolution fails.
- Cloudflare IPv4 DNS
1.1.1.1
1.0.0.1
- Google IPv4 DNS
8.8.8.8
8.8.4.4
- OpenDNS IPv4
208.67.222.222
208.67.220.220
- Google IPv6 DNS
2001:4860:4860::8888
2001:4860:4860::8844
- OpenDNS IPv6
2620:0:ccc::2
2620:0:ccd::2
- NTT/Verio IPv6 DNS
2001:418:3ff::53
2001:418:3ff::1:53
Unlike other proxies, these requests exist in their resolved form, meaning that the next time you look up these requests; you won’t have to wait for the request to be processed. This will save you from what is known as a Network Latency Delay.
Moreover, you can also use a DNS proxy to rewrite what is known as DNS proxy rules which will allow requests from different servers to be rerouted to avoid any inconvenience. However, let’s not delve into any technicalities here. The important thing to know is that this is a pretty useful proxy to use.
Web Proxy
Once in your lifetime you surely must’ve used web proxies once, a web proxy is that proxy which acts a shield between you & the website you’re visiting. It allows you to keep your identity anonymous without passing all the data to the website you’re visiting.
As explained before, when you’re visiting the site – you’re not the one actually connecting, it’s the web proxy connecting on your behalf. Hence, it will seem just as if you never visited the website at all. A web proxy is commonly used by everyone around the world to hide their identity or their searches online. Thus,
Now lots of web based proxy websites are closed, Still some of website which still live with the advertising or set up by other Proxy service or VPN service, so this should be a really old technology or known as out-date stuff, If you’re do not interested on that, you can skip this section.
Glype
Glype is one of the most used and #1 free scripts to create a web-based website, and our web.stupidproxy.com which also use the Glype, but unfortunately which already stop the updated, You can get more detail about to Glype on,
CGI Proxy
This is a pretty handy proxy and you’ll soon find out why. The Common Gateway Interface (CGI) Proxy is a proxy that appears to a user in the form of a web page. The user can then connect to different websites or access different links by means of this web page. This web page is in actuality the proxy itself and the added technical camouflage allows the user to access these websites anonymously. It works by means of an encrypted web form present on a web page. As technical as it sounds, relative to the aforementioned proxies that have been seen, it is actually quite a versatile feature to use.
It is written in the Perl Programming language and as such, it can be used on any server or computer that is capable of running the Perl Program by means of CGI. It supports a wide variety of requests and formats, such as the HTTP, Secure Socket Layering (SSL) and even the File Transfer Protocol (FTP). However, an enduring problem for this software has been its lack of availability as an open source as it comes with a licensing fee. However, it has been extensively modified to allow individuals to not only access it, but also alter it to suit their own technical needs.
Suffix Proxy
A Suffix proxy serves a pretty self-explanatory purpose. What this proxy does is that it adds its own name to the end of the URL that it is processing or rerouting. As the name of the proxy is added to the end of the URL, it is in fact a “suffix” and hence the name “Suffix Proxy”. By doing this, a suffix proxy facilitates the ability of the browser to by-pass web filters and access programs or websites. Suffix proxies offer two main functions. Firstly, they speed up access to a resource for a user. For this, they employ two further mechanisms. One is that of caching data. The other is that of saving the previous search requests of the user and retrieves that data in case the user makes a similar search in the future. The second purpose offered by the Suffix Proxy is that of maintaining the anonymity of the user.
This is done by the proxy by means of traffic filtration whereby any requests made by the user are processed by the proxy itself and are evaluated to see if this search can be linked back to the user. Suffix proxies are also far easier to use in comparison to the other types of proxies that have been seen until now. However, they are not very frequently used owing to the fact that they don’t retain a great deal of anonymity. When the proxy engages in traffic filtration, it does so by using the user’s official IP address. As a result, if it processes and passes on a request onto an external source, the external source can reach the user by means of the IP address (do note that this is not a very easy process but it is very much possible).
Advantages of using Proxy Servers
Proxy is an encrypted anonymous proxy that not only changes your IP address but also encrypts your Internet browsing sessions to keep you safe and protected with SSL, With the features of proxy server, you can not just Anonymously Browsing and more,
Proxies for Personal Use
-
Protect Your Online Personal privacy Information
-
Incognito to the Search Engines
-
Mask your Location-based on the proxy server
-
More Secure when online shopping and banking
-
Stop Tracking from your ISP
Proxies for Business Use
-
Anonymously Research Competitors
Your competitors know when you visit their website. Worse yet, based on your IP address, they can even send you to a dummy website keeping you in the dark about what they are offering. With Private Proxy, an anonymous proxy, you can make sure you see the competitors knowing that they can’t see you.
-
Bypass Restrictive Posting Limits
When you hit posting limits on websites, they are using your IP address and their cookie to block you. Bypass website limits with Private Proxy. With randomly rotating IP addresses, you get a new IP address every thirty minutes so you can continue posting.
-
Publicize Your Website Anonymously
When posting on websites, you can be anonymous so you can publicize your website as though you are a user and not the actual company. Private Proxy will mask your company’s IP address so the website and users don’t know where you are coming from.
-
Unblock Yourself from Websites that have Banned You
Companies restrict you from their website by using a combination of tracking cookies and your IP address. With Private Proxy, you can choose your location and then Private Proxy does the rest. It randomly changes your IP address every 30 minutes making it extremely hard for websites to block you.
Proxies for Travelers
-
Protect Your Wireless Activities While Browsing the Internet
Every time you connect to the Internet via a hotspot or public Wifi, all your web surfing can be viewed by the people sitting near you. With simple, and sometimes free, packet-sniffing software, criminals can see everything you transmit over a WiFi connection. By using Private Proxy, your Internet surfing is protected by establishing a secure tunnel. Private Proxy uses an anonymous proxy which is a secure tunnel that encrypts all your browser traffic so it can not be intercepted and read.
-
Defeat Criminals from Intercepting your Internet Surfing
When you connect via a public Wifi you might actually be connecting to a fraudulent hotspot. Known as an evil twin, these hotspots route all your traffic through their connection enabling them to log all your Internet communications. With Private Proxy’s secure tunnel, you can drive a connection right through an evil twin that protects all your Internet browsing.
-
Safely Connect your Browser from Your Hotel Room
When you accept the terms and conditions from your hotel they typically warn you that the connection is not secure. With Private Proxy you can secure any browser session with one click. Private Proxy’s secure tunnel protects your browsing data so no one can intercept it and read it.
-
Securely Browse from Airports, Hot Spots, and Unsecured Networks
Whether you are using the free wireless provided by an airport or logging in at your favorite coffee shop, your Internet surfing is not secure. Even if you connect your laptop as a guest on someone else’s network, you have no idea who is monitoring your connection. With Private Proxy, any browser session can be secured with only one click. Our secure tunnel shields your browsing so no one can intercept your connection and monitor you!
Disadvantages of using proxies
Up till now, the functions and types of various proxies have been discussed. However, despite all the onomatopoeically pleasing technical terms that you have heard about proxies, it does have its own negative aspects.
First up is the cache data storing system that is incorporated by most proxy service providers. It cannot be denied that this feature has greatly facilitated the searching of content from the internet and other external sources. However, the drawback of this system is that the proxy server might not be able to differentiate between what you want it to store and what you want it to save. As a result, your passwords and other private data can also be stored by the server.
We are also familiar with the use of SSL encryption by proxies to maintain anonymity. However, any hacker who is an expert in this type of language can easily hack into the web page (which is, in fact, the proxy server) and gain access to all your personal data.
In addition to this, there are several malicious or corrupted proxies who instead of returning to you the required results, load up malware and harmful data into your computer. This can severely damage your server in addition to depriving you of proper information.
Lastly, there is a moral dimension to the use of proxies. Proxies are used to access blocked or inaccessible websites. And the majority of these websites are morally hazardous to the person trying to access them. These can be pornographic websites or lucrative websites attempting to con the general public. In this case however, the proxy server itself is not to blame rather how the individual chooses to use them is what matters.
Conclusion
Therefore, we can see that proxies or proxy servers are wonderful when it comes to engaging in research-based activities. The versatile and broad categories of proxies that are available have really made it easy for people to bypass firewalls and other barriers that prevent them from accessing the resources they want.
However, the slight negativities of these proxies cannot be undermined. But it is safe to say that in the face of all the positives they have to offer, they are inherently very useful. And after reading this article, you have probably gained a good idea as to what you must look for when using or installing a proxy server.

Dear Sir,
I need a proxy for ContentGrabber (Sequentum) software:
Can your proxy be just/only configured in ContentGrabber and not really installed as a Windows software?(This is the most important thing). I don’t want it to filter any other application and I want the proxy to be within ContentGrabber enviroment only..
Wich plan is the cheapest for Webscraping?
Can you help me please?
Thank you and regards,
The most cheap solution for Web scraping,is use shared proxies which is just same as the dedicated proxies, but the IP address be shared to others, so the speed is not fast enough as dedicated IP proxy.
Also, I do know what’s your plan on your scraping, if you’re want to run a numerous request in short time, i would suggest you use the residential IP proxies, for some of big project on data scraping, such big G, amazon and Nike and so on, the proxies are easily banned by the website…
Last, You do not need to worry about the “ContentGrabber enviroment”, Now almost all proxy service which offer API for proxies, you can use the proxies on Linux, IOS, Python, PHP, C#, Java, Ruby and more…You can easily fetch your proxy servers list, and the residential proxies are more complicated but do not anxious that. the proxy provider offer great guide on how to step:), such as, Luminati.io
So in this case, Smartproxy and GeoSurf would work alright? Since those are the same as Luminati, but the following does provide mixture of residentials and datacenter IP addresses. Maybe those would work better if you do get full residential IP’s? Unless I understood something wrong.
I used Luminati, Oxylab, and GeoSurf, all of them offer both residential IPs and datacenter IPs.
And smartproxy only offer the residential IPs, those residential proxy networks usually come from the browser plugin or addon or other application, some datacenter IP may be in their residential proxy networks, but really few…maybe 0.1%.
From my experience, No one sells mixed packages:) You have to choose one package to use, Luminati’s data center IPs packages are also not cheap, and you can select only apply for one domain and share to others, can reduce your cost!
Excellent article, it is very informative. Your work is appreciated.
Hi!
I’m still deciding between a proxy or a vpn. It’s going to be mostly for day-to-day use, as I’m not into web scraping or anything of the sort. Found this article: https://www.proxydex.com/proxy-guide-for-beginner/ According to it, a vpn would suit me better, but there are so many good deals on proxies that it’s quite hard to choose!
Any help? Thanks!